Posts Tagged ‘IT Infrastructure / Networks’
Virtualization Volatility
A tech shift churches can’t ignore It’s important for leaders of non-profits — including religious organizations — to stay aware of the ever-evolving technology landscape. While these changes might not seem like a big deal on the surface, at some point they can become a big deal for every entity, both for-profit and not-for-profit. Here’s…
Read MoreReasonable & Essential BYOD Policies
BYOD– Bring Your Own Device– is an IT wave that is sweeping corporations. IT Directors are understandably uncomfortable about this. Adopting enforceable policies will make the difference, however, in BYOD’s success in any organization.
Read MoreLargest IT Outage in History
I wanted to provide an update to today’s widely reported internet outages. I hope the first thing we do when outages like this happen is to trust in the Lord. Our Savior is far more powerful than any of our technology and inconveniences like today’s outages are all part of His sovereign plan. We have…
Read MoreChurch IT – third edition released!
At MBS, advancing the Kingdom includes providing access to church IT and ministry technology resources that everyone can utilize. Regardless of whether you’re a client of MBS, these resources are available to you. Numerous complimentary resources can be found here on our website at https://mbsinc.com/articles. Our founder, Nick Nicholaou, authored a book titled ‘Church IT’…
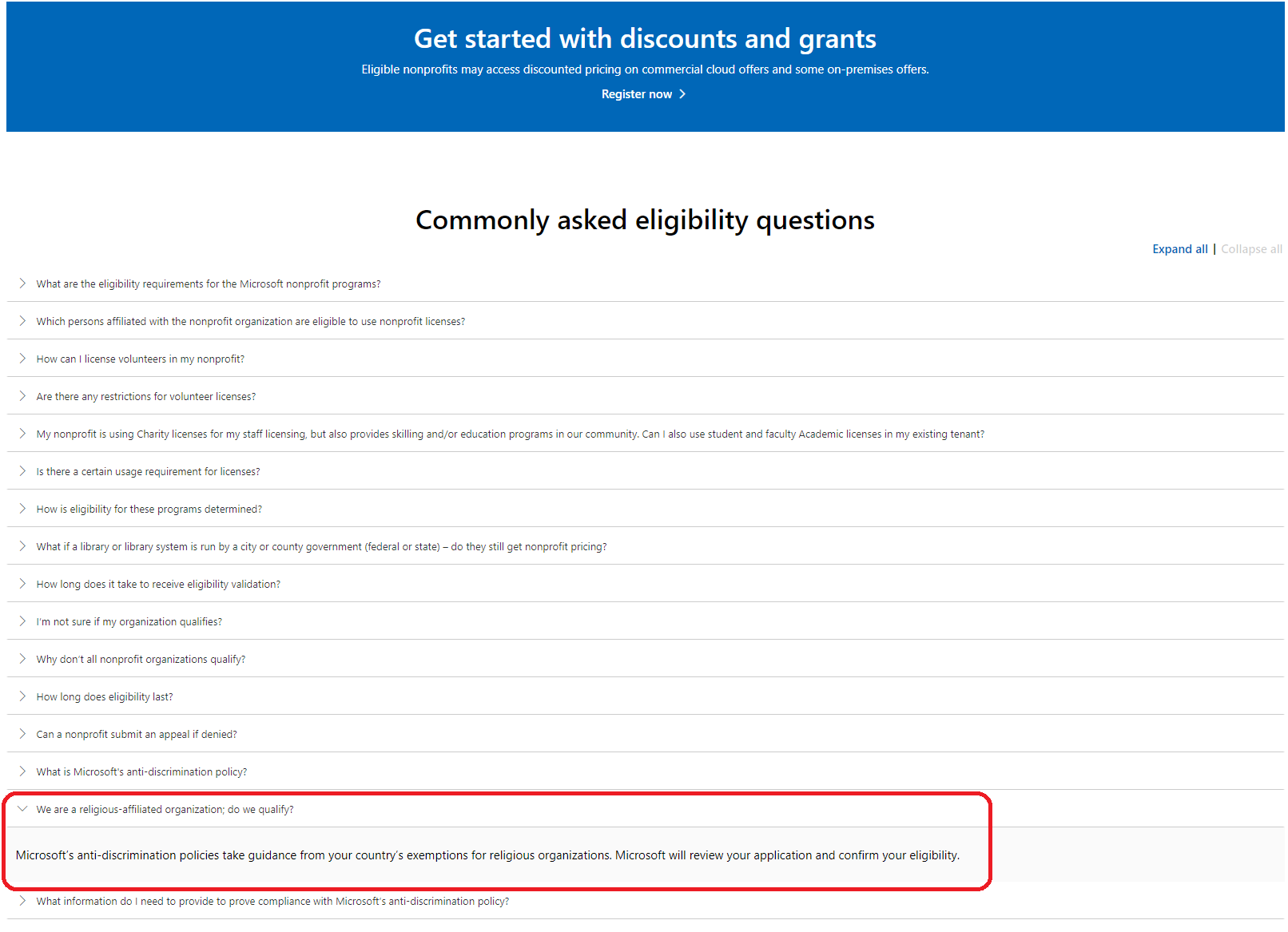
Read MoreMicrosoft Resolves M365 Charity Licensing Issue for Churches!
Many Christian churches and ministries have been uncomfortable with the Microsoft charity licensing section requiring them to certify they don’t discriminate in their employment practices regarding LGBT issues. On 10/8/2015 Microsoft resolved this and posted the changes to their website! That is great news for many! Here are the details.
Read MoreApple M1 Macs – Yes or No?
© 2021 by Nick B. Nicholaou, all rights reserved President, Ministry Business Services, Inc. Reprinted from The Church Network eJournal Apple introduced Macs with a new chipset late last year, and many are excited about it! Honestly, I am too! The specs suggest great improvements in processing power and speed, and like the Tom Cruise…
Read MoreThe Newest Technology Isn’t Always the Best Technology
Before your next tech purchase, use these three tips. © 2019 by Nick B. Nicholaou, all rights reserved President, Ministry Business Services, Inc. Reprinted from ChurchLawandTax.com Years ago, my firm researched the current tech directions and strategies in play at the time and decided to buy what looked like a very promising technology platform. It…
Read MoreGDPR and the Golden Rule
Since GDPR went into effect on May 25, 2018, I’ve been amazed at the number of questions folks are asking about it and the astonishing lack of information there is about it, especially as GDPR relates to churches and ministries.
Read MoreIdentifying, Shaping, & Meeting Team IT Needs
© 2018 by Nick B. Nicholaou, all rights reserved President, Ministry Business Services, Inc. Reprinted from MinistryTech Magazine A church IT forum discussion came up recently that is worth thinking through. The original post asked for input on how to keep team members from connecting their personal devices to the password-protected staff WiFi. The discussion…
Read MoreMarch is IT-Be-Green Month!
© 2018 by Nick B. Nicholaou, all rights reserved President, Ministry Business Services, Inc. Reprinted from MinistryTech Magazine March is the month of St. Patrick’s Day, whose modern-day associated color is green. When we think ‘green’, we also think of doing things that are friendly to the environment. What are some quick tasks we can…
Read More